The landscape of enterprise IT is constantly shifting. One of the most significant recent developments is the noticeable increase in software vendor audits, particularly from major players like Red Hat. For organisations heavily invested in Red Hat Enterprise Linux (RHEL) and its ecosystem, this trend is more than a compliance check. It is a high-stakes confrontation that demands immediate, strategic attention.
The initial shock of an audit request is often framed as a “soft audit” or renewal review. It can quickly escalate, leaving IT leaders feeling cornered with seemingly no option but to comply with the vendor’s demands.
The threatening tactic of subscription enforcement
Red Hat, now an IBM subsidiary, is increasingly leveraging its subscription model to enforce compliance across its vast installed base. The audits are designed to be comprehensive, requiring organisations to prove that every single deployment of RHEL, including virtual machines, containers, and cloud instances, is covered by a valid subscription.
The tactics employed in these audits can be aggressive and highly effective at inducing panic. The most potent threat is the cancellation of existing subscriptions for non-compliant usage. For an enterprise running mission-critical systems on RHEL, the prospect of losing vendor support, security patches, and access to the Red Hat ecosystem is a catastrophic risk. This threat acts as a powerful lever, often driving organisations into quick and costly settlements. It creates an illusion of no choice. The path of least resistance appears to be immediate, unquestioning compliance and the purchase of backdated subscriptions to cover the alleged shortfall. This is a common strategy in the software licensing world. It is designed to bypass lengthy legal battles and maximise revenue from non-compliant usage.
However, succumbing to this pressure during Red Hat subscription audits without a robust defence is a costly mistake. The initial audit findings presented by the vendor are a starting point for negotiation, not a final verdict.
The strategic alternative: The SUSE Factor
While a strong defence is paramount, the market is also evolving to provide strategic alternatives that mitigate vendor lock-in and offer leverage in negotiations. The most prominent of these is SUSE Linux. It has positioned itself as a viable and reliable alternative for organisations running RHEL and its derivatives.
SUSE’s offerings, such as SUSE Liberty Linux, provide a technology and support solution for managing and maintaining existing RHEL and CentOS installations. This is a critical development. It means that enterprises are no longer solely dependent on Red Hat for support and maintenance of their RHEL-based systems. SUSE Liberty Linux offers a path to secure your Linux future without the fear of being held hostage by a single vendor’s licensing demands. Both Red Hat and SUSE offer curated, enterprise-grade versions of the core Linux operating system, making their product offerings functionally similar for many enterprise use cases. The availability of a credible, well-supported alternative like SUSE fundamentally changes the power dynamic in an audit scenario. It shifts the conversation from forced compliance to a strategic decision about which vendor best serves long-term interests.
The true defence: ITAM and Audit Readiness
While alternatives like SUSE Liberty Linux are a valuable strategic asset, they do not replace the fundamental need for best-in-class IT Asset Management (ITAM) and a strong audit defence process. The best way to win an audit is to be prepared for it long before the audit letter arrives.
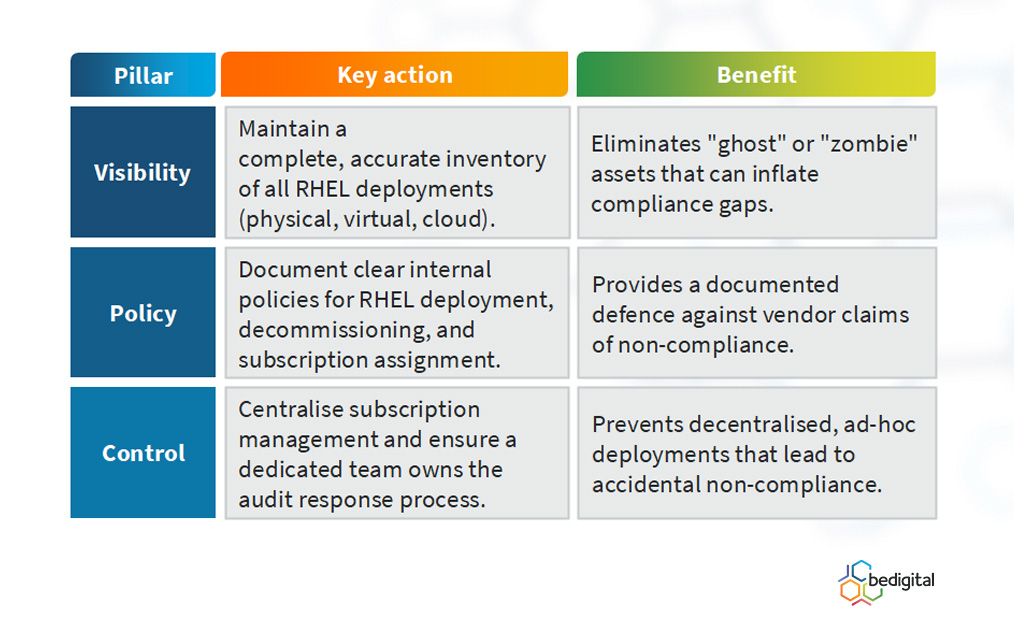
A strong audit defence is a proactive, continuous process built on three pillars:
When an audit request is received, it must be treated as a formal project. Do not ignore the request. Immediately engage senior management and legal counsel. The vendor’s initial findings should be meticulously reviewed and challenged with your own accurate deployment data. By having a clear, independently verified picture of your usage, you can negotiate from a position of strength, rather than weakness.
Conclusion
The rise of Red Hat subscription audits is a clear signal that software vendors are aggressively protecting their revenue streams. The threatening tactics, including the spectre of subscription cancellation, are designed to force rapid compliance. However, organisations have more options than they realise. Strategic alternatives like SUSE Liberty Linux provide viable support and maintenance while delivering essential negotiation leverage. However, the most effective defence is not changing operating systems, but committing to strong, consistent ITAM practices. With full visibility and control of your assets, you can move beyond compliance fear and negotiate on your own terms.


